This page is a summary of some of the cool stuff I've built or guides I've written over the years.
Check out github.com/nandan-desai-extras for more.
Contact me:Projects
Software I've built
1. BookShelf
BookShelf is a sample use case I created to showcase some of the concepts in Spring Boot and Spring Security. It is a web application with frontend built in Angular 10 and the backend server is built using Spring Boot. The project uses Spring Security, JWT authentication, reCAPTCHA v2, comprehensive validation including that for file uploads (scans the uploaded file binary to determine file format) etc. The project also covers many of the Application Security concepts. And the documentation as detailed as possible. Here for more.
2. My-Cloud-IDE
I built this for my course project in 2018. My-Cloud-IDE is a Software-as-a-Service (SaaS) built using Docker. It offers an IDE for PHP Web Development. Multiple users can login and start development and each user will be provided with an isolated environment. When a user logs in, a new Docker container is spawned and is dedicated to that particular user. Here for more. Screenshots below:
3. jWebProfile
jWebProfile is the first software I built back in July 2017. It's a desktop app built using Java Swing. This app lets the user to collect information related to people from social media accounts. Currently, jWebProfile facilitates it's users to collect information from Twitter and Github. It has features like exporting the tweets, web scraping articles, blogs etc. to fetch more information and perform analysis. Here for more. Screenshots below:
Android apps I've built
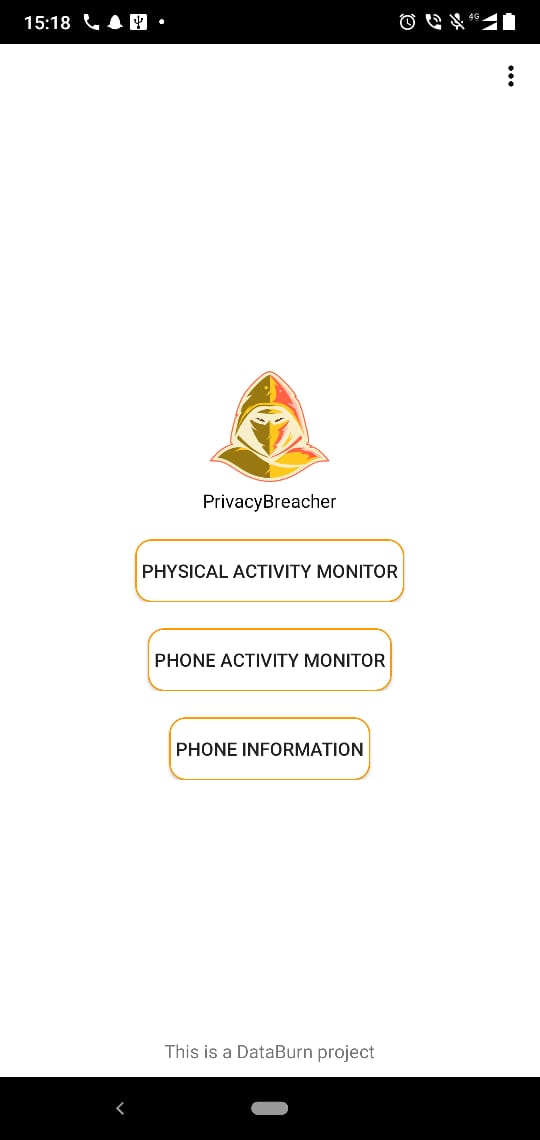
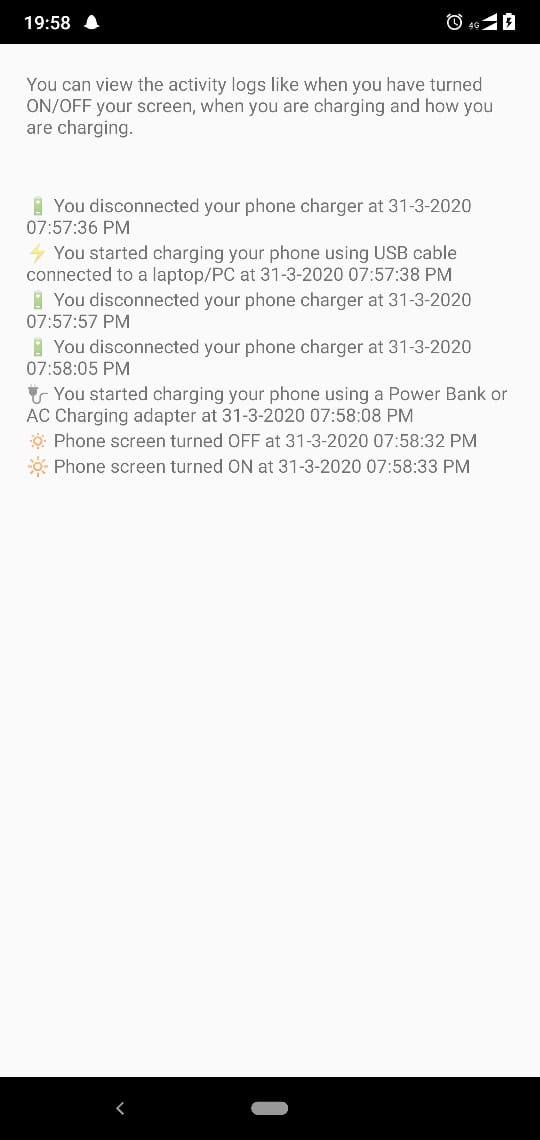
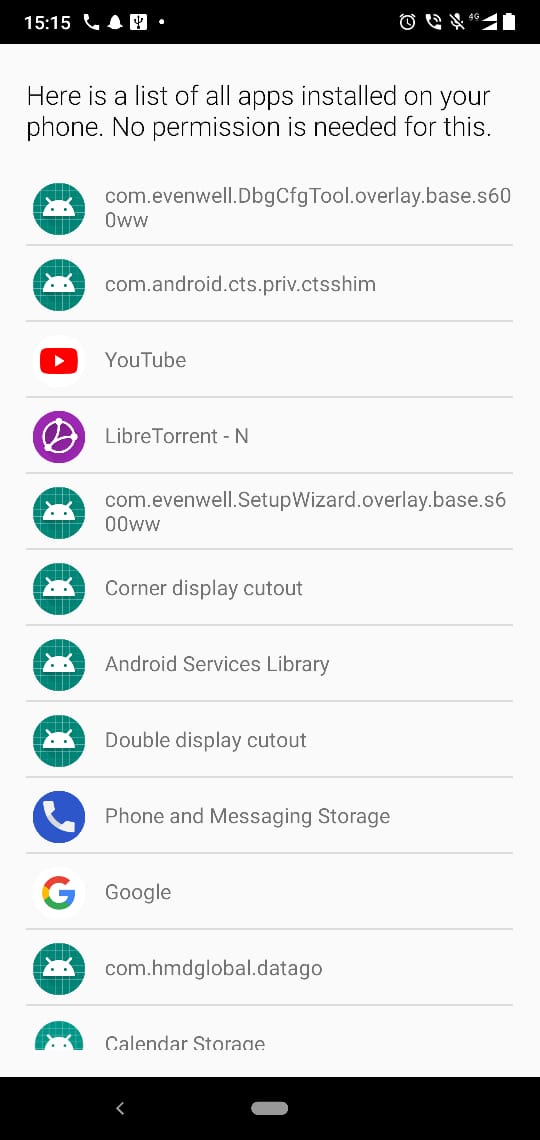
1. PrivacyBreacher
An app built to showcase the privacy issues in Android operating system. Here for more. Available on Google Play Store. Screenshots below:
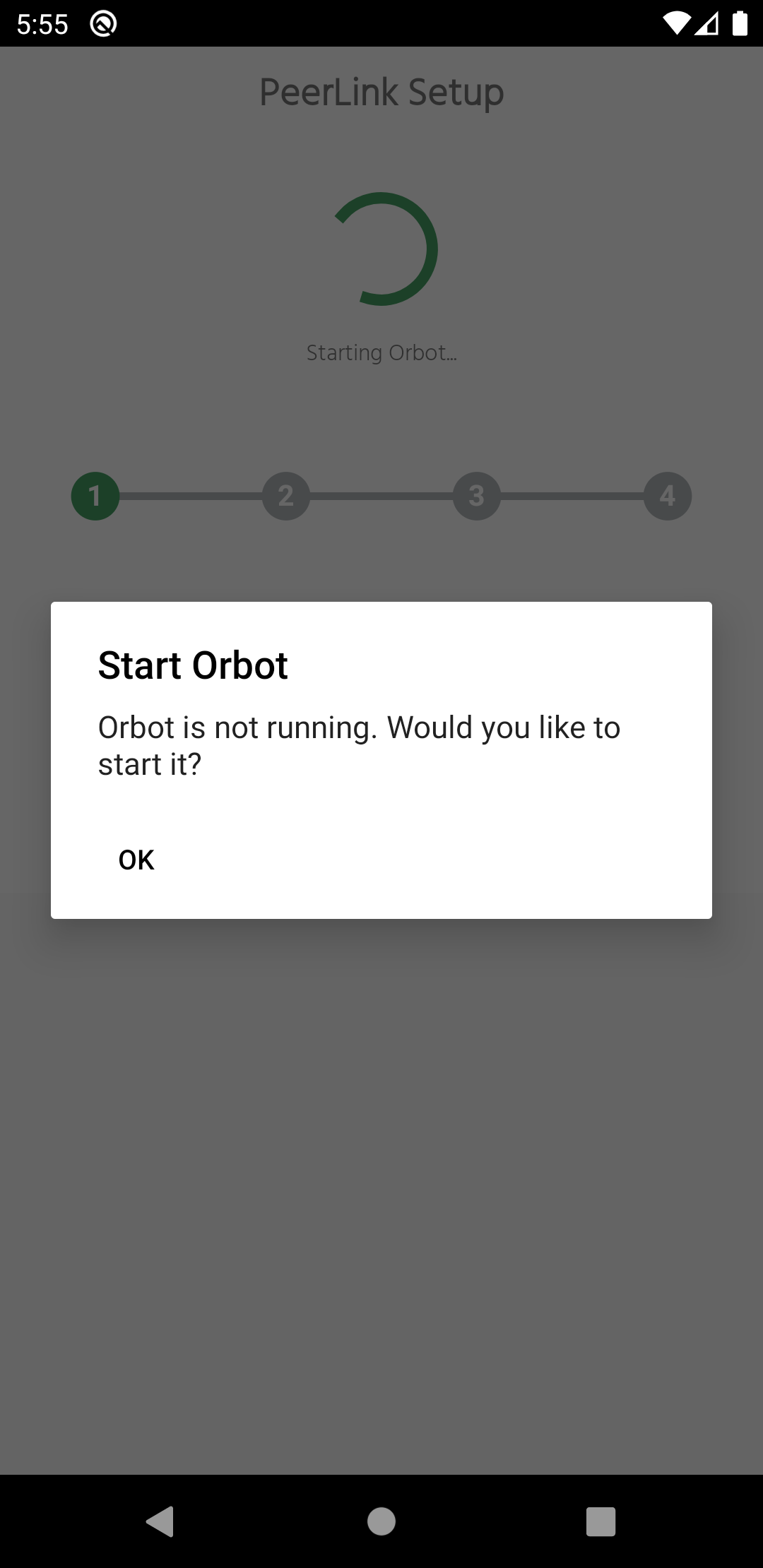
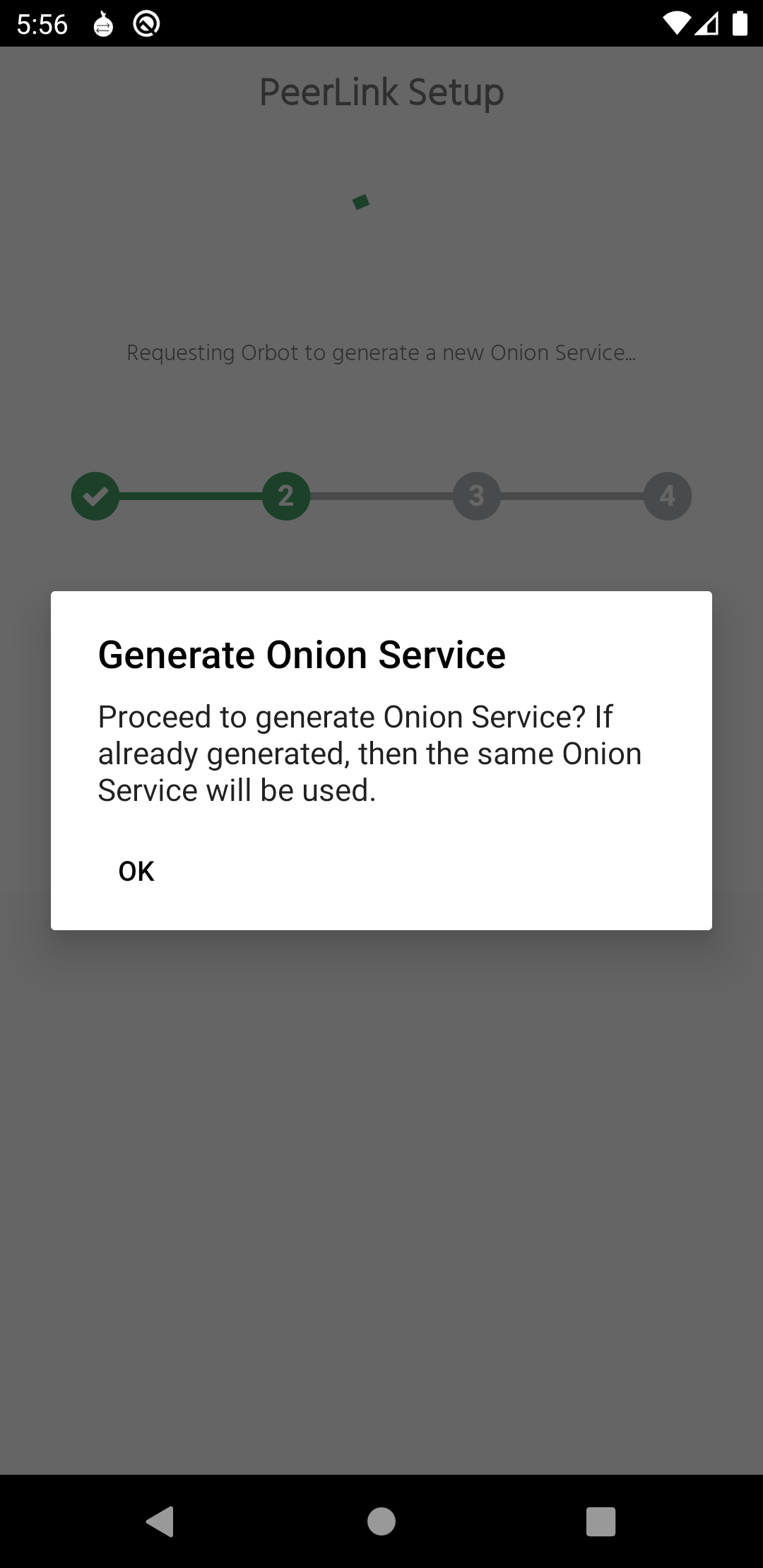
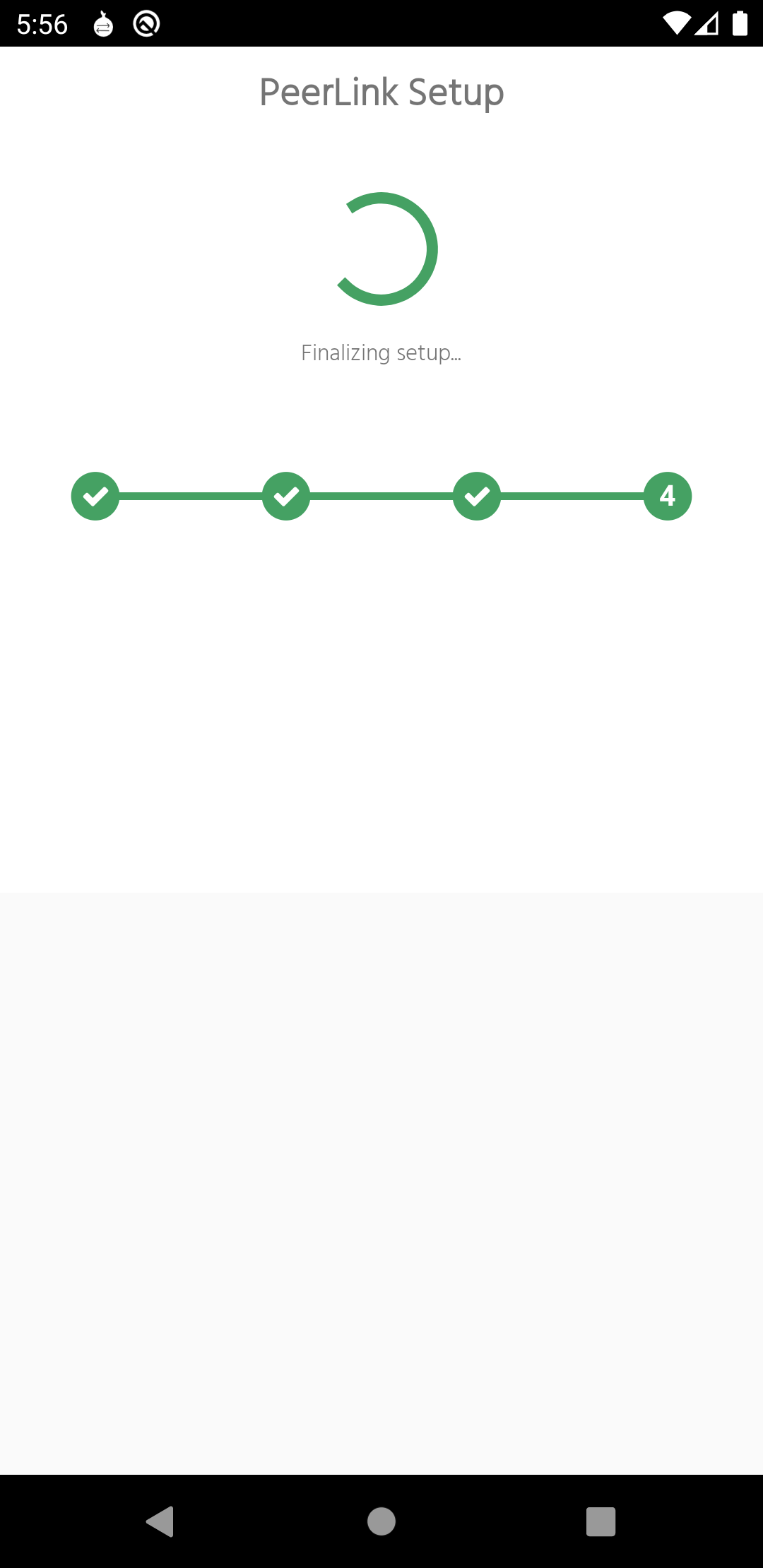
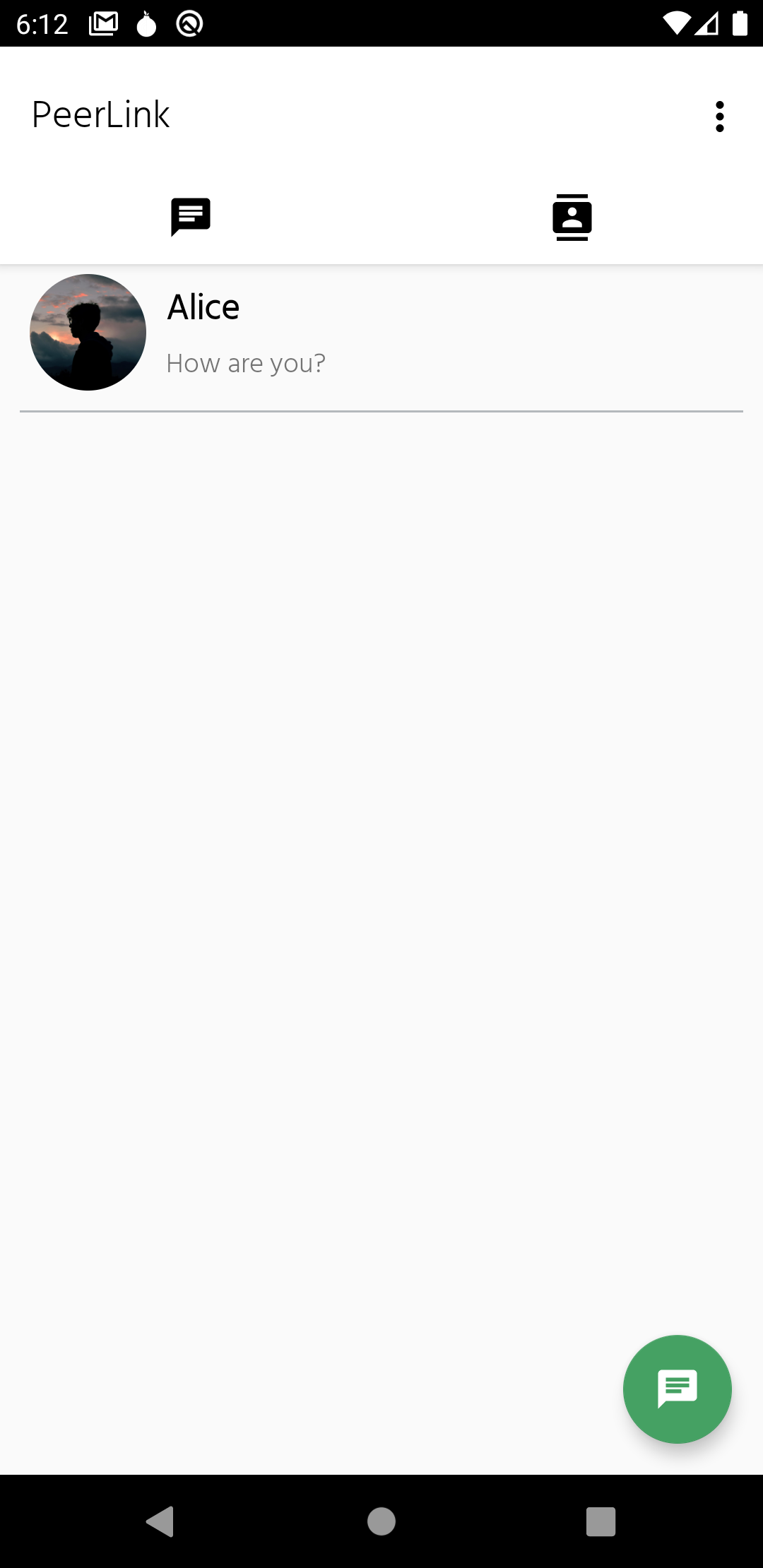
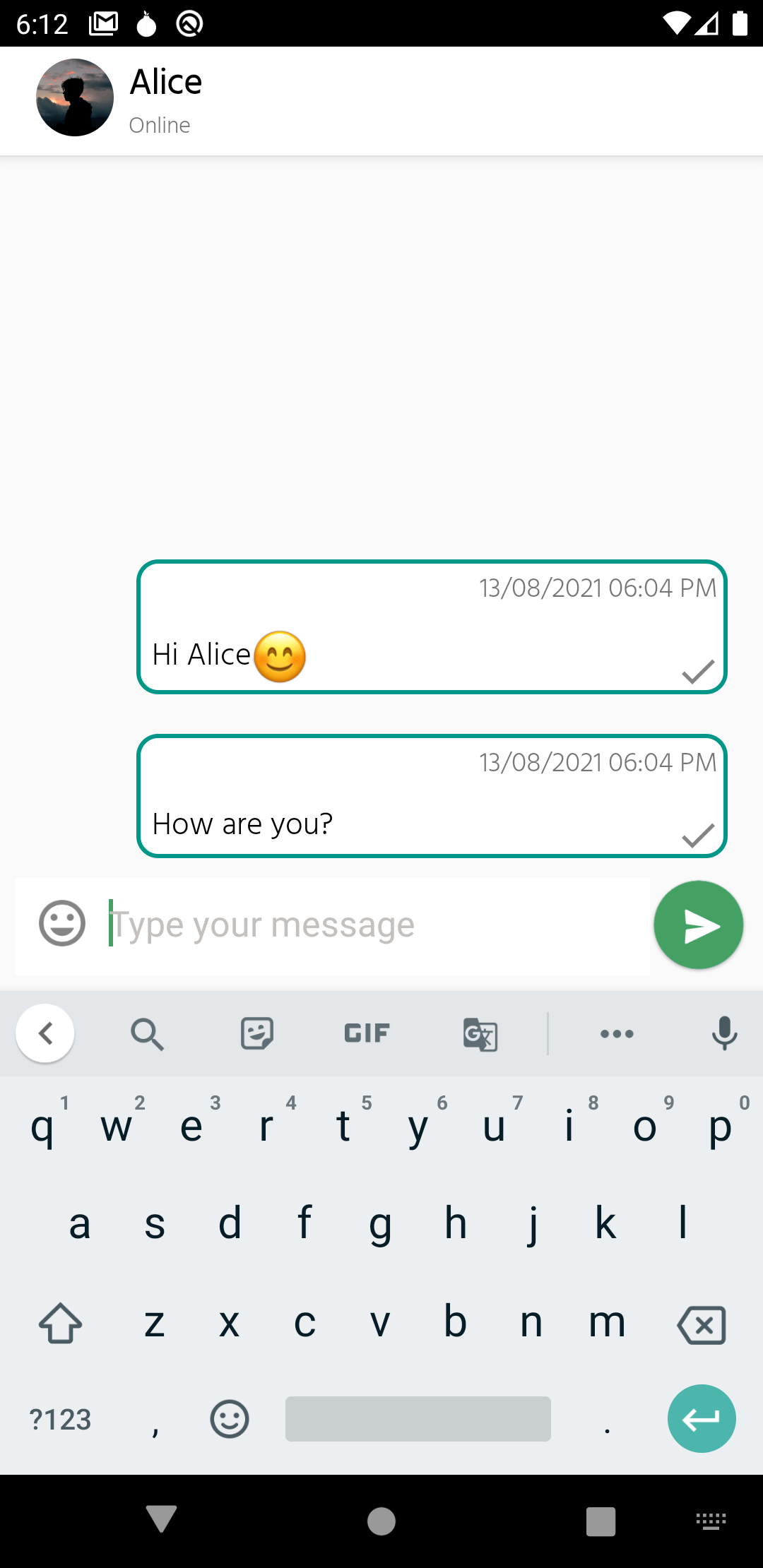
2. PeerLink
A privacy-focused Instant messaging app built on top of Tor Hidden Services. Here for more. Screenshots below:
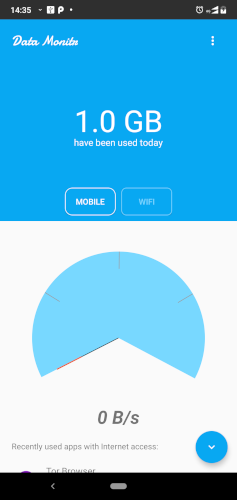
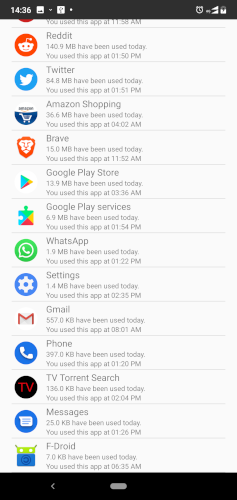
3. Data Monitr
I built this app when I was running Android Nougat. This app shows the data usage of each app, data used on Mobile/Wifi connection, live internet speed in notifications etc. Available on Google Play Store. Screenshots below:
Tried to improve this app and added a lot more features. Haven't tested it properly though. Click on this text to see the improved version of this app.
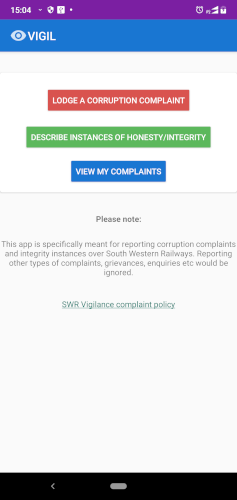
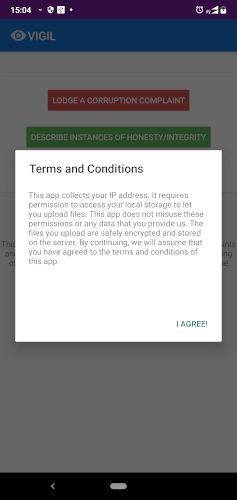
4. VIGIL
I built this app in June 2018 as part of an internship project for South Western Railway, Govt of India. I also wrote the backend for this app in PHP. Available on Google Play Store.
Software libraries I've written
1. TwitterScraper4J
This is a Java library which lets you fetch Twitter public data without the need to use any API. Here for more.
2. SocialInfo4J
This repository contains a collection of Java libraries which can be used to fetch data from popular social networks like Facebook, Instagram and LinkedIn. Might become useful in building Information Gathering tools, OSINT etc. Here for more.
3. Java-Utils
This repository contains some Java utility classes that I created for some of my Closed Source projects. Here for more.
Writeups & Guides I've written
1. AndroidIMTemplate
A brief guide on building a secure instant messaging app for Android. Covers topics like App architecture design, Security requirements like End-to-End Encryption, Database encryption etc. Here for more.
2. Android-Privacy-Issues
A detailed writeup describing various privacy issues in Android. Here for more.
3. Stackoverflow answers
I'm not too active on Stackoverflow but I've written quite a few answers on it. Here for more.
4. c-to-process
A study module where you'll be learning some very fundamental concepts related to how a simple C program becomes a Process in the Operating System. Here for more.
5. dns-works
This repository will help you understand how DNS works. It contains a technical walkthrough of the DNS resolution process. Here for more.
6. prototype-pollution
This repository tries to explain what Prototype Pollution is and will try to give you a few examples on how to use it in certain use-cases. Here for more.
7. nmap-port-scan-works
This project tries to implement the port scanning concepts described in the "Nmap Network Scanning" book. Here for more.
8. My Technical Blog
In this blog, I write some technical stuff. Here for more.
9. Windows Driver Development
This repository contains code for some simple Windows kernel drivers I created while learning about driver development. Here for more.
10. Android Reverse Engineering
In this repo, I document the things I've learnt in Android Security and Android Reverse Engineering. Here for more.
12. Building Networks
A roughly created study module to learn how to build a computer network in Packet Tracer. Following concepts are involved:
- Creating VLANs
- Configuring Trunk on Switches
- Connecting Router and a Switch with Router-on-a-Stick model
- Configuring DHCP on a Router
- Sharing routing information between two Routers
- Access Control Lists (ACLs) on Routers
- Configuring BGP
- Configuring Static Routes
Here
for
more.
Some notable course projects (CMU)
1. Computer Systems projects
Worked on several C projects/assignments in the Computer Systems course. These included:
1. Datalab: worked with binary operators in C to solve puzzle-like questions.
2. Bomblab: Reverse-engineered a binary. A classic assignment where we had to prevent the "bomb from exploding". Every "explosion" would deduct some points from our assignment score.
3. Cachelab: Learned to write CPU-cache-friendly code.
4. Malloclab: Wrote malloc-like function from scratch.
5. Tshlab: Wrote a shell (similar to Bash) from scratch. Learning about creating Processes (and handling their states), Signal Handling, etc.
6. Proxylab: Learned to write a web proxy to handle concurrent web requests and caching. Involved multithreading, tackling race conditions, etc
(I'm not publishing the source code for these projects to abide by the course policies)
2. Cyber Deception: Tools and Techniques
A course project for 'Applied Information Assurance' where me and my team showcased various methods of deceiving an attacker. The methods included creating fake ports, fake services, honeypots, etc. The logs of the attacker's activities were collected in Elasticsearch and viewable through Kibana (the ELK stack).
Project report document.
3. Designing an Ideal Filesystem for Digital Forensic Investigations [Research Paper]
Note: This is a research paper completed as part of an assignment for the Host-based Forensics course.
Abstract: Digital forensic investigations rely heavily on the authenticity and reliability of digital evidence, but recent cases of fabricated evidence have raised questions about the effectiveness of current forensic tools and procedures.
This research paper introduces IdealFS, a file system designed specifically for digital forensic investigations. IdealFS provides strong attribution and non-repudiation for each file and directory in the file system, and ensures forensic soundness by requiring cryptographic signature verification for all file system operations.
Project report document.
4. USB Mouse Firmware
My teammate and I built this project as part of 14-642: Introduction to Embedded Systems.
The files published in this repository were part of a larger project of building a fully functional Real-Time Operating System (RTOS). I'm not publishing the other source code of that project to abide by the course policies.
Project repository.
5. Network Forensics project
A group project where my teammates and I created a scenario of a small business being attacked by a ransomware and how we used various monitoring tools to construct a timeline of events and the source of the malware.
We used a real instance of Wannacry ransomware, had setup Sysmon on the victim's PC, Snort and pfSense as our firewall, Email server and the ELK stack for gathering logs from all the systems.
Project report document.
Cybersecurity educational initiatives
1. picoCTF 2023 Challenge Development
Developed a web CTF challenge called "Java Code Analysis!?!" that was attempted and solved by 1,950 CTF players (as of Jan 2024). This challenge requires you to go through the server code written in Java and use Burpsuite to understand the client-server interaction. Try my challenge here.
2. picoCTF 2024 Challenge Development
Developed several Reverse Engineering, Anti-Debugging and Windows-specific challenges for picoCTF 2024.
The following are the challenges I've created:
- Classic Crackme 0x100: a 'Crackme' challenge.
- WinAntiDbg0x100: a Windows Anti-Debugging challenge. Level 1.
- WinAntiDbg0x200: a Windows Anti-Debugging challenge. Level 2.
- WinAntiDbg0x300: a Windows Anti-Debugging challenge. Level 3.
- YaraRules0x100: a challenge that involves analyzing a Windows executable file and creating YARA rules for it.
3. Udemy course: Hard-disk Forensics
Published a free Udemy course on Hard Disk Forensics where you can learn about the basics of several key components; including Filesystems, The Sleuth Kit (TSK) tools (the backbone of Autopsy), Partitions, Partition Tables, Partitioning Schemes, Data Link standards like ATA and SCSI (with a focus on ATA), and more. Here for more.
My contributions to other projects
1. cloudflare-scrape-Android
Helped to reduce the library size of this repo. Here is my accepted pull request.
2. Tor-Onion-Proxy-Library
Added relavant details in the README and also added a sample app on how to use that library. Here is my accepted pull request.
3. torghost
Fixed a few privacy issues in this project. Here is my accepted pull request.
Miscellaneous (smaller and old projects)
1. my-backup-scripts
A python script that I created to backup my files. It works alongside rclone.
2. DemoSignal
A simple Java project showing two or more Signal instances exchanging text messages and files. This repo includes how to use Signal protocol in group as well as direct messages.
3. SimpleWebServer
A very simple web server in C.
4. DuckDuckJ
A Java library for DuckDuckGo's Instant Answer API.
5. JavaRSSParser
A Java library for parsing RSS (https://en.wikipedia.org/wiki/RSS) feeds.
6. openvpn-session
This is a small java library to manage client sessions in OpenVPN community server.
7. DVWA Docker
A repository that fixes some issues with other Dockerized DVWA (Damn Vulnerable Web App) projects.
My Social Profile
Visit my Github profile to get an overview of all my Open Source work!
Visit my LinkedIn profile here!